Sup’ PSHomies,
SIDHistory is one of those Active Directory attributes you love to hate. When migrating from one domain to another, it let’s you retain access to resources in the Source Domain. This is a great way to transition, but in my experience it also makes for quick-shift migrations.
The first thing I do whenever we start a migration is have a look at SIDHistory. This will let me know quickly what we’re dealing with:
- Has there been a previous migration? (I’ve seen objects in excess of 5 entries)
- Did they clean up? (Obviously they didn’t or I wouldn’t see any entries)
- Do I need to worry about Token-bloat?
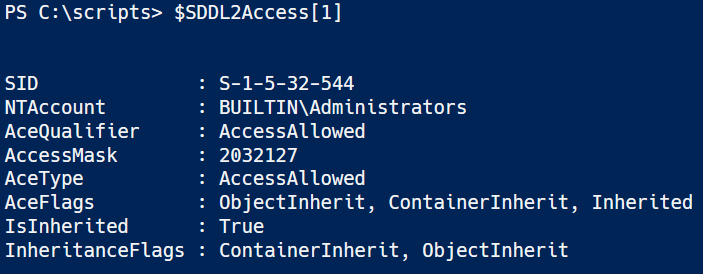
Remember the blog I did about SDDL? Well SDDL deals with access based on SIDs. When a user logs on to the system, not only the new SID, but also the old SID is retrieved from the SIDHistory attribute and is added to the user’s access token and used to determine the user’s group memberships. The SIDs of the groups of which the user is a member through either the new SID or the old SID are then also added to the access token, together with any SIDHistory those groups might have.
This is also the reason tokenbloat can be an issue if it isn’t cleaned up after a migration.
So how do you find out about SIDHistory?
| Get-ADObject -LDAPFilter "(sIDHistory=*)" -Property objectClass, distinguishedname, samAccountName, objectSID, sIDHistory | | |
| Select-Object objectClass, DistinguishedName, SamAccountName, objectSID -ExpandProperty SIDHistory | | |
| ForEach-Object { | |
| [PSCustomObject]@{ | |
| ObjectClass = $_.objectClass | |
| DistinguishedName = $_.DistinguishedName | |
| SamAccountName = $_.SamAccountName | |
| SID = $_.ObjectSID | |
| DomainSID = $_.AccountDomainSID | |
| SIDHistory = $_.Value | |
| } | |
| } | | |
| Out-GridView -Title "AD Objects with SIDHistory" |
On the subject of removing SIDHistory
This is tricky. Having and keeping SIDHistory intact will keep many a pesky helpdesk calls at bay… But is it wise to keep it?
From a Data (Read NTFS) perspective, you’ll need to Re-Acl your data structure. If you’ve kept you NTFS ACLs (Access Control List) nice and tidy (Wait, gimme a second to catch my breath from laughing) then you’re golden! This has never been the case in all my migrations so far. My advice when it comes to Re-Acl, is to recreate the data structure (empty) and assign the correct ACEs (Access Control Entry) to the ACLs. Maybe I need to explain what Re-acl a bit more…
Re-ACL is the process of translating SIDs on Resources. I first came across the term using Quest Migration tools. This gave me the option to:
- add the target SID to a resource
- replace source SID on said resource
- remove source SID from resource if everything is working
Here are the things you need to consider for each option
Adding the targetSID to a Resource
This gives the AD Object access without having to rely on SIDHistory. This means that once the target SID has been added you can safely clean up SIDHistory. A target SID can only be added if a valid source SID has been found. I’ve seen too many ACLs with unknown ACEs in migrations I did over the years. This does nothing to clean up those unknown ACEs. Adding a target SID will expand you ACLs, which can have an impact on processing time
Replacing the sourceSID on a Resource
This makes for a cleaner ACL. Again, this does nothing for unknown ACEs. Replacing adds the targetSID and removes the sourceSID in the same process. A bold move, reverting SIDHistory isn’t as easy a writing to other AD object attributes and for good reason.
Remove sourceSID from Resource once everything has been verified to be working
Most are quite content that everything is working and don’t bother with this. Again, if your structure is up to date, this shouldn’t be an issue. What I’ll usually hear is: “We’ll create a new structure later on and get that cleaned up…” This rarely happens…
To wrap up
SIDHistory is a great way to retain access to source Resources, just make cleanup a part of the migration (If possible).This will vastly improve tokensize and improve your security
Re-Acl only makes sense if you’re content with your current NTFS data structure. If not, then I’d suggest redefining your Data structure. It’s a chore but well worth it.
Hope it’s worth something to you…
Ttyl,
Urv